Android is the most popular operating system. It is safe and pretty much stable. But sometimes new vulnerabilities show up. Some of them are very dangerous. The Bluebox Security research team recently found a new vulnerability on Android. The bug is called Fake ID which allows hackers to steal data and sometimes remotely control the phone.
This bug is more dangerous than others because the malware doesn’t need the user permission to take over the phone. The vulnerability allows malicious applications to impersonate trusted applications without any user notification. The vulnerability can be used by malware to escape the normal application Sandbox and take malicious actions. It can insert a Trojan horse in any application by impersonating Adobe systems.
Also Read: How To Fix TowelRoot “Phone Isn’t Supported” Problem
It can gain access to NFC payment and financials by impersonating Google Wallet. It also can control the entire device by impersonating 3LM. Fake ID exploits Android method of handling identity certificates which verifies that an app is what it pretends to be.
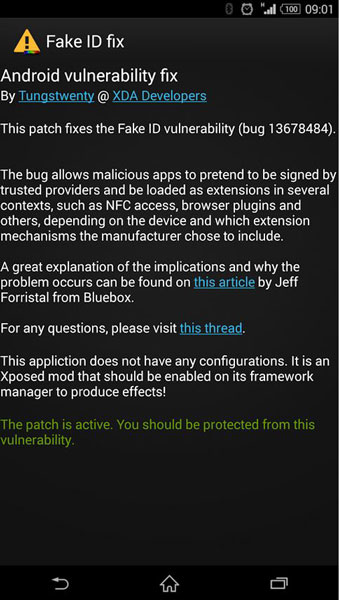
This bug allows hackers to create their identity certificates, then a claim is issued through certificate authority. Attackers make an application with the malicious identity certificate and create a certificate authority claim.
Also Read: How To Find, Track, Lock and Rescue Your Stolen/Lost Android Device
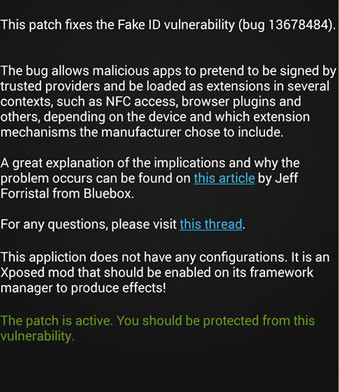
The Fake ID vulnerability can affect all Android devices. To fix this you have to download the package from the Xposed repository. Download it here. It is also available on Play Store. Install it as a normal application, enable the module on Xposed Installer and then reboot your phone.